Cybersecurity – complex threats, Zero Trust and secular growth
Date 21 July 2021
Type Alternative Asset Management
“Article 2/4 on disruptive tech trends. See the previous note on Digital transformation”
Source: Cowen
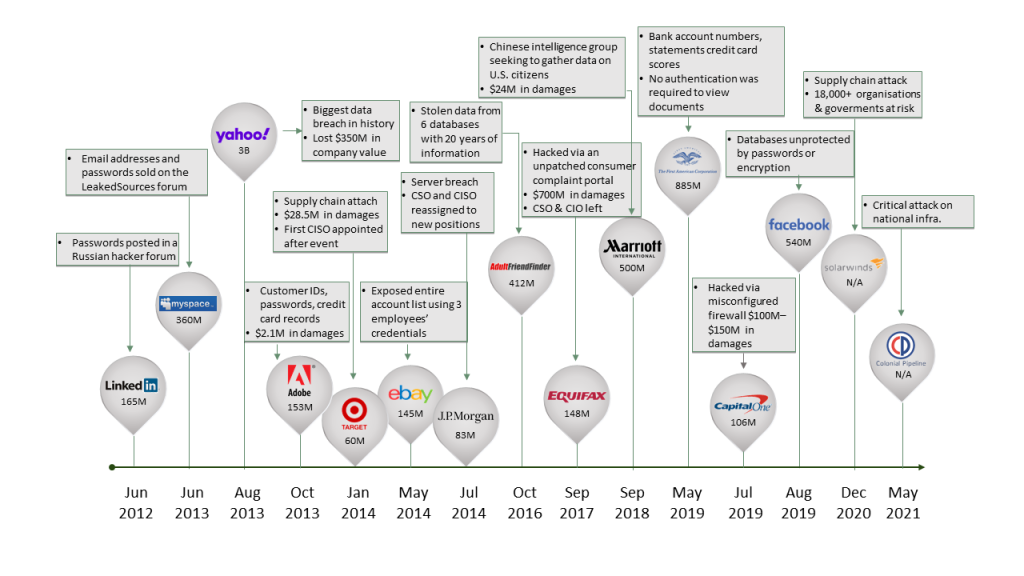
In a world where more transactions have shifted online and more data is processed at home for corporate purposes, cybercriminals (with increasing sophistication of cyber threats) see more opportunities to steal, disrupt or destroy data. In 2020, we saw hackers targeting high-profile organisations with significant datasets, particularly in the retail, supply-chain, finance and public sectors (Solarwinds, Microsoft, Equifax and in the last two months Colonial Pipeline and Kaseya). Indeed we note that recent data from RiskIQ highlights the cost of E-commerce losses due to online payment fraud stand at $38,000 per minute. The indirect effect of the rapid shift to remote work, digital transformation is that more companies are pushing their computer networks onto the cloud, elevating the importance of cybersecurity budgets. We see cybersecurity businesses that typically account for 15-20% of AGTF portfolio clearly benefitting from this.
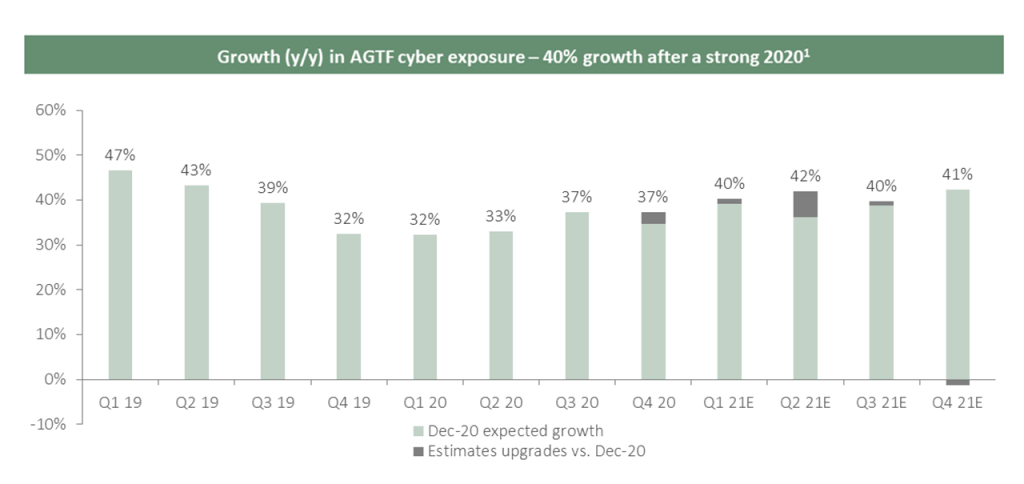
Source: AGTF. Calculated as a weighted average of quarterly y/y growth of the AGTF portfolio’s cybersecurity companies. (1) Revision of growth estimates don’t reflect any change in weights and/or positions in the portfolio, it is a like-for-like comparison of the portfolio estimates as of the end of December 2020 vs June 2021.
The timing of attacks is sophisticated and designed for maximum chaos at times of distress. We believe this leads to sustainable growth in the cybersecurity industry. Some of the drivers of this growth are:
- Technology outpaces security features. New technologies and innovation are rapidly evolving, making the sophistication of attackers more effective.
- Cloud adoption creates new risks. Cloud creates new risks as it removes the traditional physical network perimeter, particularly for hybrid environments.
- IoT adoption creates new challenges. The rise in the adoption of IoT exponentially increases the number of connected devices and the network size, while also increasing risks.
- New actors are growing. There is a rise in nation-state threat actors (China, Russia, Iran, Ukraine and North Korea) who are targeting corporates in the US and Europe.
- Talent shortage will continue to exist. We believe there is a shortage of 3m-4m cybersecurity engineers globally.
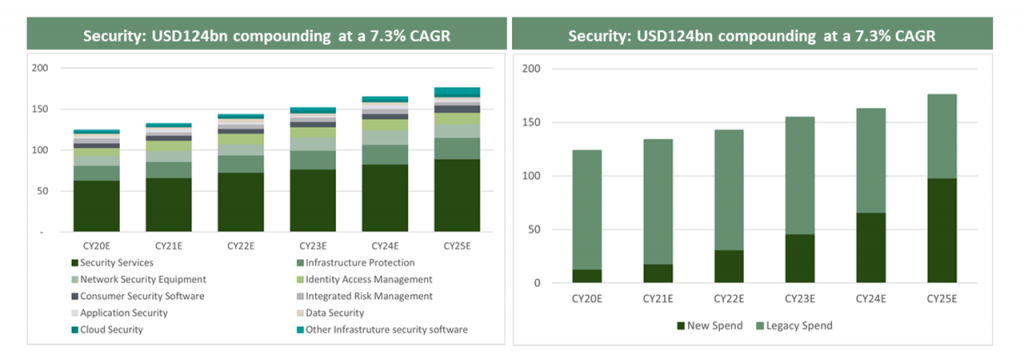
Source: Gartner “Forecast: Information Security and Risk Management, Worldwide, 2018-2024, 1Q20 Update”.
Alantra Global Technology Fund Team
*This article is an extract from the fund’s 2021 outlook letter. If you would like to be added to the fund’s distribution list contact [email protected]
This is article contains information (the “Information”) of Alantra Global Technology Fund (hereinafter, the “Fund”), a subfund of Canepa Funds ICAV, and it has been prepared by Alantra EQMC Asset Management, SGIIC, S.A. (hereinafter, “Alantra AM”). Alantra AM has not obtained an independent verification regarding the accuracy and integrity of the information used, nor a confirmation of the reasonability of the hypothesis considered. The Information has implicit subjective judgements. In particular, most of the criteria are based in estimates of the Fund’s future results. Considering the inherent uncertainties regarding any information concerning the future, some of these hypotheses may not materialize as defined.
The Information is not an offer to buy, sell or subscribe for securities or financial instruments and is not intended to be investment advice. Any decision to buy or sell securities issued by the Fund subject to this Presentation should be based on the legal documentation of the relevant Fund, in particular the subscription agreement and the prospectus of the Fund and the Key Investor Information Document (KIID) as it is filed with the applicable regulatory authorities from time to time, or on publicly available information on the related companies. The recipients of the Information must bear in mind that the securities or instruments discussed in herein may not be suitable for their investment objectives or financial circumstances, and past performance should not be taken as a guarantee of future performance. The Fund is an UCITS fund under the 2009/65/EC Directive.
In light of the above, neither Alantra AM, its officers, directors or employees, or its shareholders, may be held in any way liable for damages that could arise, directly or indirectly, as a result of decisions taken on the basis of this Information or any use given it by its recipients.
